CSPs face an increasingly complex array of external compliance
requirements from their customers, whether those include industry
standards, regulatory regimes, or customer-specific frameworks.
Frequently, those requirements are based on or refer to industry
standards. As a result, using industry standards can be an effective
compliance approach for CSPs if they can navigate through the
ever-increasing number of standards that exist or are under development
(see Figure 1).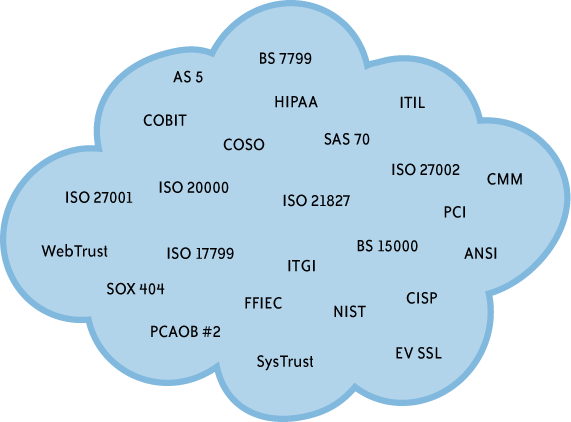
From an information technology and security controls perspective, it
can be helpful to look at these standards in terms of their focus and
objective. The matrix in Table 1
was developed to summarize how a number of leading industry
standards/regulatory requirements fit together. Understanding these standards in their proper context helps
an organization to determine their applicability and how they
might be used.
Table 1. High-level standards road map
| | Control environment/company level
controls | Information security | IT service delivery/operations | Systems development | Financial reporting systems | Specific technologies or incremental
requirements |
|---|
| Best practices
Guidance | COBIT |
| COSO | ISO27002 | ITILISO 20000-2 | CMM/ISO 21827 | ITGI-SOX | ISO various ANSI various NIST
various |
| Certification/audit
criteria/requirements | | ISO 27001 | ISO 20000-1 | |
| Regulatory/industry
requirements | | FFIEC HIPAA HITRUST NIST PCI ISO
2700X | | SOXPCAOB | EV SSL |
| Audit
framework | SAS
70 SysTrust WebTrust BITS
FISAP | PCAOB | WebTrust CA WebTrust
EV GAPP |
As Table 1 shows, many IT
standards have a specific area of focus, such as:
Overall control environment/company-level controls
Information security
IT service delivery/operations
Systems development
Financial reporting systems
Specific technologies
In addition, the nature of individual standards can generally be
characterized as:
When developing a controls framework or assessing how to address the
requirements of a particular standard/set of requirements, it is desirable
to base the framework on the standard that is most relevant. For CSPs,
where security is a paramount concern, ISO 27001 is used as a baseline.
The CSP may refer to ISO 27002 for additional best practices guidance. It
may then be necessary to add to the control framework incremental
requirements from relevant regulatory or industry requirements or topics
covered in the illustrative control objectives. As the CSP enters new
markets or industries and inherits new requirements, it is essential that
the CSP critically analyze such requirements to determine whether they
truly give rise to needed additional controls or whether they are already
covered by the CSP’s control set. Relevant audit frameworks should be
considered when designing the CSP’s control set and periodic external
audits should cover the most relevant aspects of the CSP’s
controls.
The following sections discuss a selection of common
industry/regulatory requirements (Sarbanes-Oxley, PCI DSS, HIPAA) and
their applicability in a cloud computing environment.
1. Sarbanes-Oxley Act
In response to significant financial reporting fraud in 2001–2002, the
Sarbanes-Oxley Act of 2002 (SOX) was passed and signed into law. As a
result of SOX:
Public company CEOs and CFOs are required to certify the
effectiveness of their internal controls over financial reporting
(ICOFR) on a quarterly and annual basis.
Management is required to perform an annual assessment of its
ICOFR.
External auditors are required to express an opinion on the
effectiveness of management’s ICOFR as of the company’s fiscal year
end.
SOX also led to the creation of the Public Company Accounting
Oversight Board (PCAOB) which was charged with establishing audit standards.
PCAOB Auditing Standard No. 2 called attention to the importance of
information technology general controls (ITGCs). The following paragraph gave rise to public companies’
renewed focus on the effectiveness of their ITGCs:
Some controls ... might have a pervasive effect on the
achievement of many overall objectives of the control criteria. For
example, information technology general controls over program
development, program changes, computer operations, and access to
programs and data help ensure that specific controls over the
processing of transactions are operating effectively.
Ultimately, the IT Governance Institute developed a set of IT Control Objectives for
Sarbanes-Oxley that became the de facto industry standard for ITGC
needed to achieve the requirements of SOX. This included control
objectives and recommended supporting control procedures in the
following areas:
Program Development and Program Change
Acquire or develop application system software.
Acquire technology infrastructure.
Develop and maintain policies and procedures.
Install and test application software and technology
infrastructure.
Manage changes.
Computer Operations and Access to Programs and Data
Define and manage service levels.
Manage third-party services.
Ensure system security.
Manage the configuration.
Manage problems and incidents.
Manage data.
Manage operations.
From an IT perspective, key application controls supporting
financial reporting processes would also be within the scope of a
company’s internal and external SOX compliance efforts.
PCAOB Audit Standard No. 5 in 2007 emphasized a risk-based
approach, thereby enabling most companies to narrow the scope of their
SOX compliance activities. Although SOX applies to U.S. public companies
with a certain market capitalization, the concept has also been adopted
in Japan (J-SOX), in the insurance industry (NAIC Model Audit
Rule), and elsewhere.
1.1. Cloud computing impact of SOX
SOX focuses on the effectiveness of a company’s financial
reporting process—including finance and accounting processes, other
key business processes (e.g., the order-to-cash process), and controls
over IT systems that have a material impact on financial reporting
(e.g., the company’s enterprise resource planning or ERP system and transaction processing systems that feed
into the general ledger). The scope includes internally managed
systems and outsourced systems that can materially impact financial
reporting. The SOX compliance scope for each public company is
ultimately defined by the company’s management with input from its
external auditor. Whether or not a CSP becomes relevant to a specific
corporate customer’s SOX audit activities will depend on the nature of
service provided by the CSP to that corporate customer.
Services provided by a CSP could be relevant to a corporate
customer from a SOX perspective. For example, an organization might
utilize a SaaS application that plays a significant role in financial
reporting serving as the system of record for various transactional
activities. If those transactional activities are financially
significant to the customer, the SaaS application would likely be part of the customer’s
SOX scope. As a result, the customer and its external auditor would be
required to test relevant CSP controls—by performing test procedures
at the CSP site, reviewing the CSP’s current audit report, or a
combination of both. Such controls would typically include the
aforementioned topics and may include application controls as
described shortly.
In another scenario, an organization might utilize PaaS to underlie an important financial application. An
organization might use IaaS to support traditional applications or
cloud-based applications that are used for processing or reporting on
financial transaction activities. In each of these cases, SOX control
requirements would be applicable.
From an IT general controls perspective, it is important to have
robust processes for user management/segregation of duties, systems
development, program and infrastructure change management, and
computer operations (e.g., monitoring, backup, and problem
management). Effective IT general controls are imperative to enable
application controls.
Application controls will vary depending on the nature of the
application. Typical controls focus on segregation of duties for key
functions, completeness and accuracy of reports, system configurations
for transaction processing, logging of activities, and so on.
In addition, it is important for the CSP to clearly define which
control activities are the CSP’s responsibility and which are the
responsibility of the customer. Consequently, the CSP and its
customers need to define boundaries where there is shared
responsibility. This enables the CSP to focus its compliance efforts
on areas it controls, while helping customers to do the same.
Where the CSP supports services that are likely to be in scope
for SOX, the CSP should build those key controls into its control
framework and provide guidance for customers as to how the CSP helps
the customer otherwise meet its compliance requirements.